As an application penetration tester, it is not uncommon when scoping an engagement for a prospective client to ask if we test “according to an OWASP Top 10 Methodology.” To this I answer “yes, of course,” but what I would really like to do is explain why the question does not make sense. Hopefully, this post can now fulfill that role.
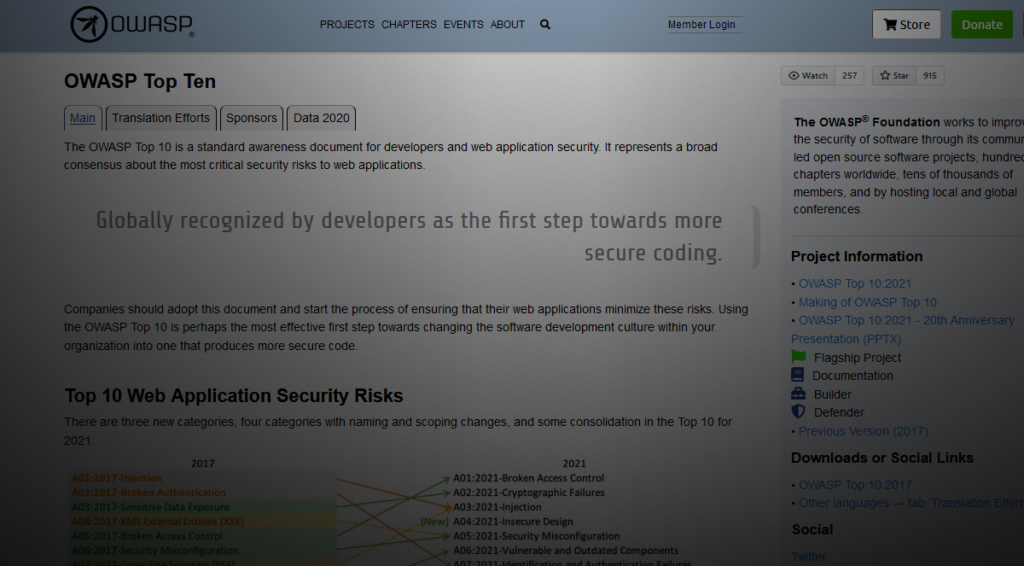
The OWASP Top 10, at a high level, is quite simple: it is a list of the top risks facing web applications broadly. The primary intent is clearly stated by the maintainers: “The OWASP Top 10 is primarily an awareness document.” Here are the things the OWASP Top 10 is not:
- A security testing methodology
- The top 10 risks posed to your application specifically
- A standard for secure coding or developer education
- A list of all possible risks posed to web applications
If you need evidence of the final point in this list, simply examine the CWE mappings for each of the Top 10 items. If you tally each mapping, does it sum up to the 933 weaknesses (CWEs) tracked by MITRE? It does not.
Even so, despite the intent of the project, “this has not stopped organizations from using it as a de facto industry AppSec standard since its inception in 2003.” OWASP further notes that “it is the bare minimum and just a starting point.” How widespread is this issue? If you search for “owasp top 10 methodology” you will find no shortage of security consultancies offering application penetration testing according to this so-called methodology.
If I am being charitable, I would assume that much of this content was developed and deployed by sales or marketing folks rather than security professionals, but I know this is not always the case. Perhaps part of the issue is that the industry reinforces this poor understanding by including “OWASP Top 10” testing or methodology as a prerequisite on job postings. I cannot change how other firms manage their hiring, but I personally would prefer not to see “OWASP Top 10” on a resume.
So what is the OWASP Top 10 good for? For new entrants into the application security space, it may be a useful reference to begin investigating and understanding the biggest contemporary risks. It may also be a useful reference in some situations when prioritizing security efforts, but I cannot immediately think of a valuable use case. For me, the Top 10 is interesting and I appreciate the effort that goes into the project, but it does not provide practical value to my testing efforts.
We will, of course, continue to reference it within our technical findings. The clients want it, after all.